A message that appears to be from Netflix says, “Your membership has expired, click here to renew.“ An email that looks like it’s from Amazon tells you, “you have a refund due to a system error, click here to update your information and receive $50.” What do you think might be an electronic bill from your phone provider states, “You haven’t paid last month’s bill. Pay attached invoice as soon as possible to avoid penalties.”
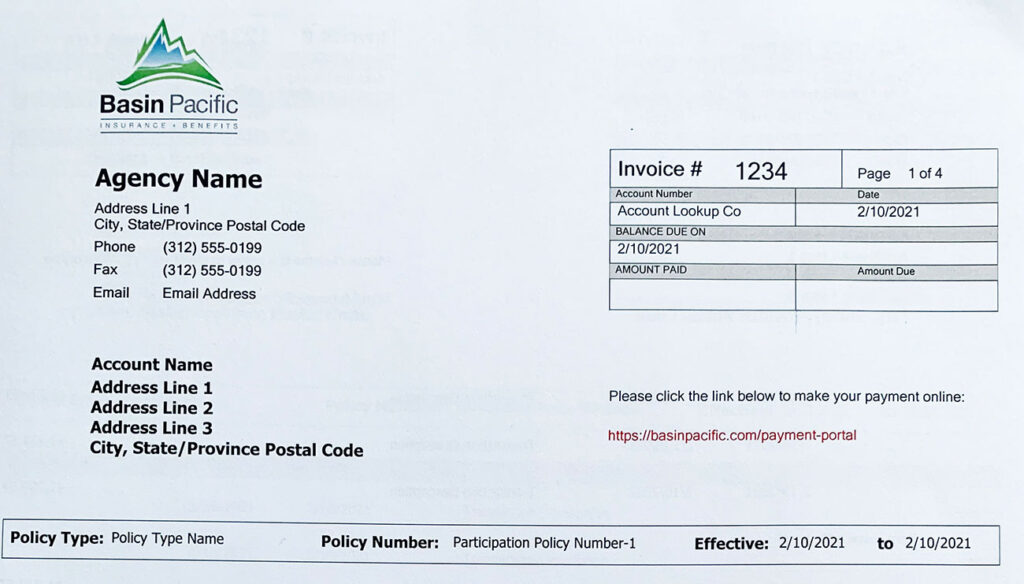
These are all imposter emails known as phishing. Fishing emails take advantage of our human makeup by creating a connection, lowering our guard, and then hooking us to give away personal information— user names, passwords, or credit card information. This manipulation is accomplished by the impersonation of someone or something we trust, the creation of a sense of urgency, and the focus of our attention on something we want or need. The attackers use stolen logos or common email templates to make their work look believable. They include a call to action such as “Click Here “or “Log Into Your Account” to instill a sense of urgency. Sadly, on the other side of that action, the attacker is waiting to steal your information and identity. Keep reading to learn about types of phishing scams and how to protect yourself.

Types of Phishing
Account activity
The company is reaching out to confirm your account information, alert you that your account has been locked, or inform you that more information is needed.
Membership updates
A company you may or may not have a membership with is contacting you about restarting or deactivating your service. Or, they may be alerting you that your account has been logged into from a “new browser.” According to KnowBe4, “Deactivation in process” is the most used email subject line.
Credential phish
you receive an email asking you to log into your account. Seems harmless enough, but this attack is coming from a fraudulent source, even though it appears as normal as any search engine. It is a productive scam because with a simple tweak to the HTML attachment that is commonly used by financial institutions, they can get through your antivirus software. For example, bankofamrica.com—did you catch it?
Packaging
A recognizable company that you have received packages from in the past wants you to verify your shipping address or fix an issue with payments. With online shopping as prevalent as it is today, “A delivery attempt was made“ is the second most clicked phishing campaign according to KnowBe4. For example, a message from UPS is alerting you that you missed a package delivery and need to click on the tracking number to locate it. You will then be taken to a different webpage, where you are expected to hand over information about yourself or the delivery address.
Unexpected money
It’s your lucky day! Somehow, the company you just had a transaction with, or even the IRS, made a mistake, and you are due for some money. Or, perhaps, a stranger wants to give you something for free— all you need to do is send a small amount of money or information.
The best way to defend yourself online is to know what you are looking for!
Phishing scams are ever-changing, and with each successful new tactic, you can expect ten more to be created.
Think before you click, and if it smells phishing, ask these questions:
- Is this for me? Who is the email addressed to, and where did it come from? Do you even have a connection to the source or the senders address?
- Why would they ask me that? No true company that you work with will ever reach out and ask you does your password or ask you to change it through an email. You would initiate that process yourself after logging in.
- Am I really that lucky? No one has a rich cousin or friendly Nigerian prince who wants to give them a pile of money. This is also the case when an email is giving you money. If it feels too good to be true, it probably is.
- Why does it look so sloppy? Professional organizations spend a lot of time and money on their brand. When you receive an email begin to look for misspelled words incorrect information or a browser that doesn’t match the one you use for your actual account.
- Where’s the fire? Any email that is trying to create a sense of urgency by putting you on a clock is simply using a scare tactic to disarm you. Why are they trying to get you to act so quickly? A real company has an entire department to help with your questions.
For more information on cyber security, click here
Excerpt from Your Money Vehicle: How to Begin Driving to Financial Freedom! by Jedidiah Collins







Leave a Reply
You must be logged in to post a comment.